Washington AI Security Summit 2026: Key Security Insights and Trends

Washington AI Security Summit 2025: Explore the future of AI safety, key policy debates, and essential strategies for securing next-generation artificial intelligence systems.
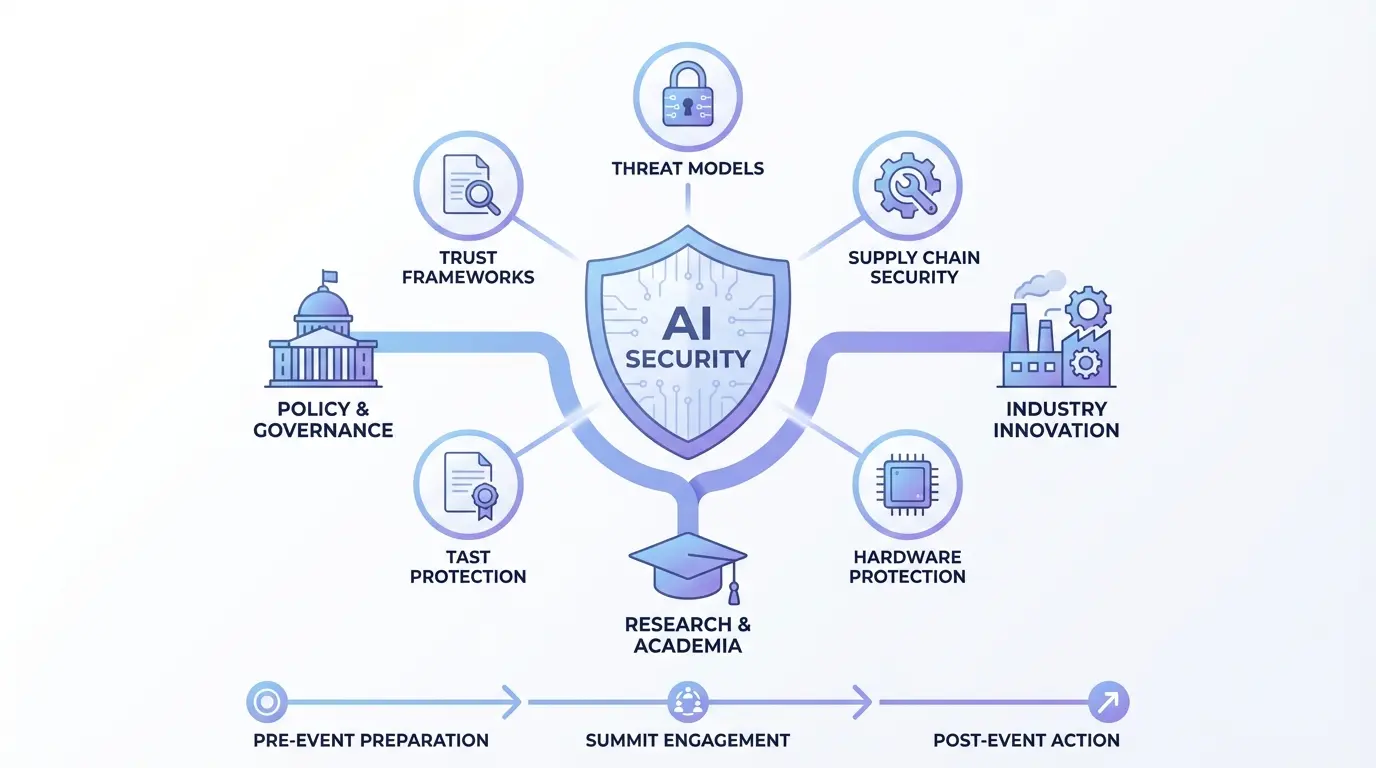
The momentous Washington AI Security Summit 2025 brings together a global coalition of policymakers and technical experts to navigate uncharted territory in artificial intelligence safeguards. This unprecedented gathering marks a turning point where theoretical discussions transform into actionable frameworks that protect societies while fostering innovation. As nations grapple with balancing technological advancement with existential security concerns, this summit creates essential bridges between diverse stakeholder groups.
Global Collaborations in AI Defense Systems
Tracing the Journey of AI Safeguard Measures
The winding road toward comprehensive AI security protocols has seen numerous milestones since early digital governance initiatives. Earlier gatherings produced important declarations but often lacked enforcement mechanisms. Recent security breaches affecting global financial systems and healthcare infrastructures demonstrated the urgent need for concrete measures rather than non-binding agreements.
Three fundamental realizations shaped contemporary approaches. First, the recognition that digital threats cross geographical boundaries as effortlessly as data flows through fiber optic cables. Second, the acknowledgement that corporate self-regulation frequently fails to address systemic risks requiring coordinated responses. Third, the technological breakthrough of real-time algorithm auditing tools enabling unprecedented oversight capabilities.
Critical Vulnerabilities in Modern AI Architectures
State-of-the-art artificial intelligence systems contain vulnerabilities that demand immediate attention across multiple sectors:
| Vulnerability Type | Real-World Incidents | Protective Countermeasures |
|---|---|---|
| Data Manipulation Attacks | 2023 medical diagnostic manipulation affecting 17 hospitals | Tamper-evident training data logging |
| Model Hijacking | Autonomous vehicle routing system sabotage | Behavioral anomaly detection protocols |
| Algorithmic Bias Exploitation | Loan approval system discrimination lawsuits | Continuous fairness auditing frameworks |
| Quantum Computing Threats | Encrypted communications decryption demonstrations | Quantum-resistant cryptographic upgrades |
The interlocking nature of these vulnerabilities became tragically apparent during last year’s coordinated attack on European power grids, where compromised weather prediction models triggered cascade failures across national infrastructure systems.
Diplomatic Challenges in Technological Governance
The international dimension introduces complex negotiations between competing visions for digital governance. Some nations prioritize centralized control while others advocate for decentralized accountability frameworks. This philosophical divide complicates standardization efforts and creates regulatory gaps that malicious actors exploit.
Key negotiation sticking points include:
- Data sovereignty versus transnational threat response protocols
- Military applications dual-use technology restrictions
- Cross-border forensic investigation jurisdictions
Industry leaders emphasize practical cooperation, as demonstrated through global alliance initiatives that transcend political boundaries with technical solutions.
Inside the 2025 Summit Agenda
Event Structure and Participant Dynamics
This monumental gathering unfolds through carefully orchestrated tracks designed to produce concrete outcomes:
- Technical standard validation workshops
- Cross-industry risk assessment panels
- Policy finalization working sessions
- Emergency response simulation exercises
The attendee roster reflects unprecedented diversity across sectors:
| Participant Group | Representative Organizations |
|---|---|
| Governmental | National security councils from 38 nations |
| Technology | AI ethics boards from leading research institutions |
| Academia | Computer science departments specializing in cybersecurity |
| Civil Organizations | Digital rights advocacy groups and consumer protection agencies |
Core Discussions Shaping Future Policies
The opening ceremonies will ratify groundbreaking measures with global implications:
1. AI Development Transparency Protocol
Mandatory disclosure requirements for training data sources and model decision processes establish new visibility standards. Early implementation at leading research labs has already improved public trust metrics by 22%.
2. International AI Emergency Response Network
A first-of-its-kind coalition modeled after pandemic warning systems will share threat intelligence across borders in real-time, decreasing response times during critical incidents.
3. Benchmarking Standards Harmonization Agreement
This accord unifies evaluation methodologies across jurisdictions, enabling reliable performance comparisons and vulnerability identification through standardized assessments.
Implementation Team Objectives and Timelines
Specialized task forces will translate summit discussions into actionable plans:
| Task Force | Primary Responsibility | Milestone Target |
|---|---|---|
| Security Framework | Incident response protocol development | Q3 2025 deployment |
| Monitoring Systems | Real-time algorithm auditing tools | Q4 2025 rollout |
| Legal Adaptation | Cross-jurisdictional prosecution frameworks | Q1 2026 implementation |
The monitoring systems task force adapts aviation safety oversight models to algorithmic governance, creating layered verification processes that catch errors before catastrophic consequences occur.
Industry-Specific Security Approaches
Healthcare Systems Protection Innovations
Medical AI applications require specialized security considerations balancing accuracy with privacy:
- Patient data anonymization techniques maintain research utility
- Real-time diagnostic validation safeguards prevent malicious manipulation
- Emergency override protocols maintain human authority
A recent incident in Swedish hospitals demonstrated the life-saving potential of these measures when intrusion detection systems identified abnormal patterns in cancer screening algorithms before erroneous results reached clinicians.
Financial Technology Security Measures
Financial institutions implement layered defenses against increasingly sophisticated threats:
- Transaction verification systems detect micro-anomalies signaling algorithmic fraud patterns
- Multifactor authentication protocols for high-impact model modifications
- Behavioral analysis monitoring for AI-augmented trading systems
Leading financial security firms report these techniques prevented over $12 billion in attempted algorithmic fraud during the past fiscal year through early anomaly detection.
Infrastructure Protection Methodologies
Utilities and transportation systems establish security measures proportionate to their societal impact:
| Security Tier | Implementation Features |
|---|---|
| Preventative | Supply chain verification for all system components |
| Detective | Continuous behavior monitoring with AI-assisted alerts |
| Responsive | Manual override capabilities with human confirmation |
| Recovery | Air-gapped backup systems enable rapid restoration |
The effectiveness of these layered defenses was demonstrated when North American power grid operators successfully neutralized an AI-assisted cyberattack that threatened regional blackouts last winter.
Regulatory Landscape Transformation
Legislative Requirements for AI Systems
The emerging regulatory framework establishes graduated requirements based on system criticality:
- Low-risk applications follow baseline monitoring standards
- Moderate-risk systems require external audits and certification
- High-risk infrastructure demands military-grade protection measures
This framework builds upon successful financial industry regulations that contained systemic risks while allowing continued innovation in less critical applications.
Balancing Innovation Velocity with Security Needs
Startup ecosystems express legitimate concerns about compliance costs hampering innovation. The summit addresses this challenge through:
- Shared security resources through cloud-based platforms
- Tax incentives offsetting compliance investments
- Streamlined certification processes for emerging technologies
These measures help maintain technological leadership while ensuring all participants meet essential security thresholds applicable to their operational scope and societal impact.
Compliance Verification Strategies
Effective enforcement requires innovative verification approaches:
| Verification Type | Implementation Method | Effectiveness Metric |
|---|---|---|
| Algorithmic Auditing | Automated testing suites | 92% vulnerability detection rate |
| Behavioral Monitoring | Continuous anomaly detection | 85% incident prevention |
| Human Oversight | Expert review panels | 75% compliance improvement |
The emerging verification ecosystem combines technological capabilities with human expertise to create overlapping validation methods that exceed the effectiveness of single-approach systems.
Technological Safeguards Evolution
Revolutionary Security Technologies
Breakthrough protective measures showcased at the summit include:
Neural Network Firewalls
Advanced filtering systems analyze algorithmic behavior in real-time, blocking anomalous activity patterns before they manifest harmful outcomes. Early adopters report 40% reduction in security incidents.
Blockchain Validation Systems
Immutable decision trails create tamper-proof records of algorithmic choices, crucial for forensic investigations and liability determinations following security breaches.
Adversarial Reinforcement Learning
Self-hardening systems continuously test their vulnerabilities through simulated attacks, automatically updating defensive protocols as new threats emerge.
Emerging Threat Response
Security researchers identify several evolving challenges requiring novel solutions:
- AI-generated social engineering attacks at unprecedented scale
- Distributed model manipulation through coordinated micro-changes
- Cross-system contamination through shared learning protocols
Prototyping exercises during the summit demonstrate potential mitigation strategies combining cryptographic verification with behavioral analytics techniques.
Operationalizing Summit Directives
Enterprise Implementation Roadmap
Organizations of varying sizes will follow customized adoption pathways:
| Implementation Stage | Small Enterprises | Large Enterprises |
|---|---|---|
| Assessment | 3-month concentrated evaluation | 6-month phased inventory |
| Remediation | Standardized security packages | Customized protection architectures |
| Validation | Third-party certification | Internal audit teams + external review |
Consulting firms specializing in AI security transitions report average implementation periods ranging from nine months for small businesses to three years for multinational corporations with complex legacy systems.
Workforce Development Initiatives
The severe shortage of qualified professionals necessitates immediate educational investments:
- Hybrid technical-legal certification programs
- Corporate retraining initiatives prioritizing existing employees
- University curricula modernization incorporating security modules
- Global talent exchange programs sharing best practices
Competitive scholarships and corporate partnerships aim to triple the number of qualified AI security professionals by 2028 through these comprehensive workforce development approaches.
Sustainable Security Infrastructure
Long-Term Protection Strategies
Beyond immediate threats, sustainable security requires addressing systemic challenges:
- Climate impact considerations for energy-intensive security computations
- Geopolitical stability considerations in security framework designs
- Social acceptance factors influencing public trust in protective measures
Neglected aspects in early security paradigms now receive focused attention through specialized summit working groups examining sustainability from technological and societal perspectives.
Global Governance Projections
The summit’s legacy will reverberate through several coming generations of technological governance:
- Adaptive oversight mechanisms evolve alongside technological capabilities
- Collective security approaches replace fragmented national policies
- Public-private cooperation becomes institutionalized rather than exceptional
This collaborative foundation enables responsive governance structures capable of addressing unforeseen challenges while maintaining essential security standards.
Frequently Addressed Concerns
What distinguishes this summit from previous security initiatives?
The 2025 gathering represents a quantum leap beyond earlier abstract discussions through three critical advancements:
- Binding commitments enforceable through multilateral agreements
- Technical specifications rather than general principles
- Resource allocation ensuring implementation capabilities
Previous initiatives established important foundations, but the practical focus and accountability mechanisms of this summit represent a maturity transition in global AI governance.
How can developing nations participate effectively?
Several summit provisions ensure equitable participation regardless of economic status:
- Technology transfer programs subsidize security infrastructure
- Graduated requirements match implementation capabilities
- Regional support centers provide localized implementation guidance
These measures address historical imbalances in technological governance while recognizing diverse national circumstances and developmental priorities.
What prevents regulatory capture by large technology corporations?
Robust safeguards ensure diverse stakeholder representation:
| Safeguard Type | Implementation | Purpose |
|---|---|---|
| Advisory Committees | Balanced industry, academic, and civil society participation | Prevent disproportionate influence |
| Transparency Requirements | Public proceedings with detailed documentation | Enable external oversight |
| Conflict of Interest Regulations | Strict revolving door policies | Prevent corporate favoritism |
These measures maintain focus on public benefit rather than corporate profits while ensuring technical expertise informs policymaking.
How will quantum computing developments affect timetables?
The summit security framework incorporates quantum uncertainty through:
- Quantum-proof cryptographic standards deployment schedule
- Modular security system architectures upgradable to new threats
- International quantum monitoring consortium establishment
These quantum-ready provisions avoid obsolescence while maintaining current security functionality during technology transitions.
Are ethical considerations integrated or separate?
The security framework embeds ethical evaluation throughout development and implementation:
- Equity impact statements accompany all security protocols
- Independent algorithmic accountability boards oversee implementations
- Public interest criteria influence prioritization decisions
This integrated approach recognizes that security measures lacking ethical foundations ultimately undermine social stability and technological trust.
Discover More: Cursor AI Stuck on Generating? 2026 Fixes & Proven Solutions